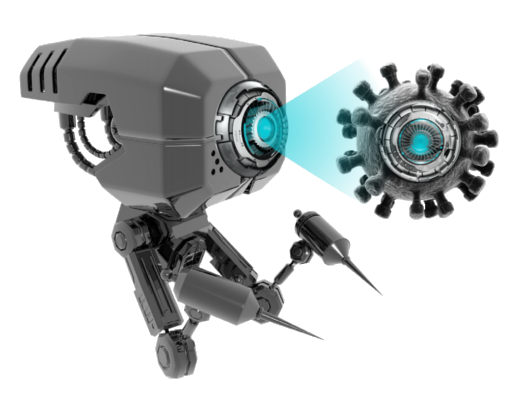
N‑able EDR is powered by SentinelOne® technology, which received stellar performance in the MITRE Engenuity™ ATT&CK® Evaluation of endpoint protection platforms four years in a row.
Nestec partner portal
All important information at your fingertips. Access the partner portal or register if you don't have an account open.
Offers, Invoices, Licenses
All important documents in one place. You can download your offers, invoices, and licenses at any time.
Online orders
You can order all your licenses directly through nestec web-SHOP.
NESTEC Partner Login
- +385 (0)1 5790321
- info@nestec.hr
- Book a meeting